CT-011: Decoy wallets with seed offset passphrase in Monero CLI
This is the 11th report in the Cypherpunk Transmission series.
Motivation
There is a rather simple, yet underrated method of adding some basic Evil Maid protection to your wallet seeds while gaining some plausible deniability in the process.
This short practical guide uses encrypted_seed in Monero CLI to create a decoy XMR wallet.
Assumptions
1. Access Monero wallet
In a terminal, open any Monero wallet, and display the seed:
seed
That command should display your wallet’s 25-word seed on the screen:
exit daily below pockets biweekly unsafe winter copy sickness glass ferry sleepless code fibula mobile tether system hacksaw tail winter innocent sowed haunted irony ferry
2. Add offset passphrase
Let’s add an offset passphrase by running:
encrypted_seed
After entering your wallet password, you will be prompted to Enter optional seed offset passphrase, empty to see raw seed:
I am going to use a random passphrase:
skylabelroundgrade
Note: it is recommended to use a 6 to 8 (english) words as a seed offset passphrase.
Enter your seed offset again, to confirm.
The new transformed seed will be displayed:
woozy kangaroo darted lordship governing mighty cocoa emulate value economics gang oyster upgrade sowed cuisine innocent gusts bakery mirror vague highway apex afoot algebra value
This is your decoy wallet. The passphrase offsets the original seed in a reproducible way and you will need both the new seed and the passphrase to decrypt the original seed.
Make sure to securely store (CT-103) both the transformed seed and the passphrase (separately if possible).
Note: the second seed is valid, but worthless to anybody who doesn’t also know that passphrase.
3. Restore original wallet
To access the real wallet, type in:
monero-wallet-cli --restore-deterministic-wallet
When asked to Specify Electrum seed:, paste in your transformed seed and press Enter.
Next, enter your seed offset when the Enter seed offset passphrase, empty if none: prompt appears.
Input a new password for the wallet and confirm it. Optionally, also enter the restore height and wait for the sync.
You now have access to your original seed. Delete the wallet, restore it, and test everything thoroughly before using with larger amounts.
Anyone that tries to restore the wallet from the second, transformed seed, without knowing the offset passphrase will just get access to the empty (decoy) wallet.
Observations
- if you forget or lose your offset passphrase, your seed alone won’t be enough to recover your funds
- note that this is not true encryption for seeds
- consider your own threat model (CT-0014) before using this functionality
- it is possible to create multiple decoy wallets
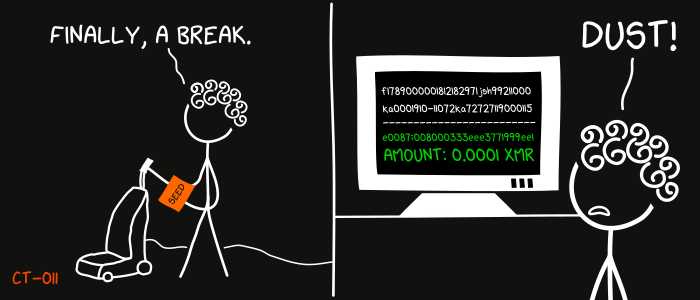
- optionally you could transfer some XMR to the decoy wallets for some extra blackmail protection
- the feature is also available in Monero GUI Wallet, Monerujo (CryptSeed)5, MyNero Wallet6
- test adding and subtracting seed offset passphrases by using the Transform Seed functionality on monerotech.info7’8
That’s it. I am very interested to know if you find this method useful.
Feedback
Let me know if you find this helpful and, depending on interest, I will do my best to post a new Cypherpunk Transmission report every (other?) Monday.
Questions, edits and suggestions are always appreciated @ /about/.
-3RA
Credit goes to gnuteardrops from monero.graphics for the amazing xkcd graphic. Work and xkcd Script font licensed under CC BY-NC 3.0.