CT-010: Managing passwords, keys, and seeds
This is the 10th report in the Cypherpunk Transmission series.
Motivation
Passwords, PGP keys, SSH keys, onion service private keys, XMR wallet seeds, addresses, contacts and encrypted messages - it can be a daunting task to securely create, store, and maintain all of that private data.
This guide suggests a solution that is potentially compatible with most threat models.
Assumptions
- you’re on a GNU/Linux machine (Debian/-based)
- basic terminal knowledge
- a five dice set
- ~15 mins free time
1. Install KeepassXC
Let’s first install the KeepassXC1 open-source password manager:
sudo apt install keepassxc
2. Create database
Open up KeepassXC and hit CTRL+SHIFT+N to create a new database. The default Decryption Time, Database format and Encryption settings should be fine.
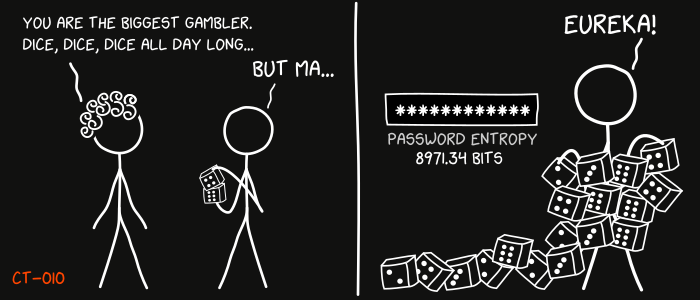
A dice-generated passphrase should be perfect for the master password.
Download any good word list file2’3’4’5. We will use EFF’s new large word list file eff_large_wordlist.txt (5 dice, 7,776 words):
curl -O https://www.eff.org/files/2016/07/18/eff_large_wordlist.txt
Roll a set of five dice all at once and write the numbers down.
Example roll:
1, 1, 6, 5, 3
Find the corresponding word for the roll with:
grep "11653" eff_large_wordlist.txt
This should output:
11653 animation
We now have the first word of our master password: animation.
Keep rolling until you generate at least 6 words (77 bits of entropy).
Example six-word passphrase:
animation approach corral stoneware blinked hardcore
Use this as your KeepassXC master password and save the encrypted database file (ie. Passwords.kdbx).
Note: you could optionally disguise the file by saving it with a random name and a more common extension (ie. styles.css).
Memorize the passphrase.
Note: if you don’t have a dice set, you can generate random passwords and passphrases in KeepassXC by clicking on the ‘dice’ icon.
3. Workflow
KeepassXC is very easy to use.
Create entries with CTRL+N or use the + icon, generate new passwords with the dice icon, copy and paste passwords from KeepassXC to websites and applications, edit entries with CTRL+E, lock the database with CTRL+L or by pressing the lock icon.
Remember to backup your database files regularly by using the Save Database Backup.. option under the Database menu.
Observations
- review your threat model6 when deciding if and how to best use the tools described in this guide
- store database backups on separate machines/devices
- whenever possible, opt for more entropy; go for 8+ word count for passphrases and 20+ characters for passwords (100+ bits of entropy)
- do not reuse passwords
- also saving passwords down on paper/metal might not fit your threat model
- consider additional security risks before using any online password managers
- it is recommended to build KeepassXC from source7
- KeepassXC can generate 2FA codes
- avoid using KeepassXC browser extensions; copy/paste instead
- a viable alternative to KeepassXC might be
pass8, the Unix command-line password manager - dig deeper: EFF9, Kicksecure/Whonix10’11
That’s it. Now you can securely create, store and maintain your private data.
Feedback
Let me know if you find this helpful and, depending on interest, I will do my best to post a new Cypherpunk Transmission report every (other?) Monday.
Questions, edits and suggestions are always appreciated @ /about/.
-3RA
Credit goes to gnuteardrops from monero.graphics for the amazing xkcd graphic. Work and xkcd Script font licensed under CC BY-NC 3.0.
-
https://www.eff.org/files/2016/07/18/eff_large_wordlist.txt ↩
-
https://www.eff.org/files/2016/09/08/eff_short_wordlist_1.txt ↩
-
https://www.eff.org/files/2016/09/08/eff_short_wordlist_2_0.txt ↩
-
https://github.com/keepassxreboot/keepassxc/blob/develop/INSTALL.md ↩
-
https://www.eff.org/deeplinks/2016/07/new-wordlists-random-passphrases ↩