CT-016: Using 1vyrain to 'soft disable' the dreaded Intel ME on xx30 ThinkPads
This is the 16th report in the Cypherpunk Transmission series.
Motivation
According to Intel, it’s Management Engine (ME) was designed for allowing businesses to remotely manage computers via Active Management Technology (AMT). The low-power computer subsystem consisting of mostly proprietary firmware is built into virtually all Intel chipsets since 2008.
Intel ME is known for security vulnerabilities and most privacy-aware users think it’s a backdoor.
Although impossible to remove completely, it can be turned off. This guide shows how 1vyrain1 can be used to soft disable Intel ME without any specialized hardware on ThinkPad xx30 machines.
Assumptions
- your system is supported2 (any xx30 series: X230/X230t/X330/T430/T430s/T530/W530)
- 1 USB flash drive
- your machine is plugged into power at all times (with a healthy battery connected)
- you have access to a Windows 64-bit install (to downgrade BIOS with IVprep if necessary)
- basic terminal knowledge
- 15-30 mins free time
- you have read and understood all of the warnings below
- you still have the guts to try this risky operation
0. WARNINGS!
Normally these kind of messages would go under Observations at the bottom of the report, but this is a special CT.
Please read this section several times, very carefully, before proceeding with this guide.
0.1 The good news
Although it is impossible to permanently brick a device with this method, you will require a hardware programmer to flash a backup or fresh BIOS after bricking.
0.2 The bad news
Losing power while flashing == 100% BRICK, guaranteed.
Before flashing, make 100% sure you know the password to your machine, even if you’ve cleared it. If you are unsure, try clearing, enabling then disabling the supervisor/BIOS password.
Setting your RAM to 1066MHz == BRICK.
There is no warranty or support guaranteed. You are THE ONLY ONE that is responsible for broken devices.
1. Check BIOS compatibility3
Reboot your machine and go into your BIOS setup by pressing the appropriate key for your model. Now find out if your ThinkPad has a BIOS version that’s vulnerable enough to be exploited with 1vyrain.
Example: for X230 machines, your BIOS should display version 2.60 or lower.
Model BIOS version
X230 2.60
X230t 2.58
T430 2.64
T430s 2.59
T530 2.60
W530 2.58
If your machine has a newer BIOS version, you will have to downgrade to a compatible version using IVprep (Step 2).
If your BIOS version is old enough, you can skip directly to Step 3.
2. Downgrade BIOS using IVprep
2.1 Prepare BIOS settings
Enter your BIOS setup and update the following:
-
Set Security > UEFI Bios Update Options > Flash Bios Updating by End-Users: Enabled
-
Set Security > UEFI Bios Update Options > Secure RollBack Prevention > Disabled
2.2 Download IVprep
Make sure you are plugged into power while running this. You WILL brick if you lose power while flashing, guaranteed.
Boot into your Windows 64-bit install, download the latest IVprep4 version from Github, extract the archive and run downgrade.bat (NOT as admin!) by double clicking the file.
You should see a message similar to this in command prompt:
Press Enter to downgrade your ThinkPad to an 1vyrain compatible BIOS version.
Press Enter to proceed. Press Yes if asked by User Account Control to allow the app to make changes to your device.
Your system should reboot in 5 seconds and you should see this:
Begin Flashing....
The system will beep repeatedly for around 30 seconds. Don’t panic, that is expected behavior.
The last message should be:
Image flashing done.
The system will automatically reboot again.
Done.
Confirm the downgrade was successful by going into your BIOS and checking the version.
If all went well, you are now hopefully looking at a BIOS version that is compatible with 1vyrain (listed in Step 1) and you can proceed to the next step.
3. Exploit BIOS using 1vyrain
3.1 Download 1vyrain
Download the latest 1vyrain version (currently Revision 55).
Check to see if hashes match:
md5sum 1vyrain.iso
Output should be exactly dd30313a8665e870360920b00cec55c4.
3.2 Create live USB
We need to burn the 1vyrain image (260 MiB) onto a flash drive.
3.2.1 On Linux
Run lsblk before plugging in the USB to display your devices.
Plug in the USB and run lsblk again. You should easily spot which one your USB is.
Note: double check to make sure you don’t erase the wrong device.
Run dd:
sudo dd if=path/to/1vyrain.iso of=/dev/sdX status=progress
Note: replace path/to/1vyrain.iso and /dev/sdX with the appropriate values.
3.2.2 On Windows
On Windows you can use Rufus6 in DD mode. No special configuration is necessary.
3.3 Prepare BIOS settings
Enter your BIOS setup and update the following:
-
Set Startup > UEFI/Legacy Boot > UEFI only
-
Set Security > Secure Boot > Off
Note: make sure your machine is set to boot from your USB (move it at the top of the list).
3.4 Exploit BIOS!
RE: Make sure you are plugged into power while running this. You WILL brick if you lose power while flashing, guaranteed.
Boot from the USB and follow the on-screen instructions.
You should be greeted with the following message:
Press Enter key to attempt BIOS exploit. Your Thinkpad will suspend as part of the process. Press the power buttong to wake it up!
Press Enter.
When your machine suspends, press the power button.
At the Please enter a choice: prompt, press 1 and Enter.
You should see this:
Press Enter key to begin flashing your jailbroken BIOS! Do NOT let the ThinkPad shut off during the process, you will need a hardware programmer to fix it!
Cross your fingers and press Enter.
You will probably have to wait for 30-60 seconds (at the Erasing and writing flash chip... status).
Finally you will see a success message:
All done! Press enter key to restart your ThinkPad or CTRL+C to exit to shell.
Press Enter.
You will get some CRC errors and reboots. All normal.
When prompted, press the appropriate key to enter your BIOS setup. Hopefully you can see a brand new Advanced tab.
4. Disable Intel ME
We can finally disable the Intel ME. I know you’ve already spotted it under:
- Advanced > ME configuration > Intel(R) ME > set to Disabled
Note: you may get a ‘Configuration Changed. Restart the system’ message. That is normal and your machine will probably restart before booting into the OS.
Observations
- X330 machines are supported but detected as normal X230 machines (the flashing menu has an additional option to flash a BIOS with the LVDS patch for machines detected as an X230)
- disabling Intel ME might not fit your own threat model7 (Intel considers disabling ME to be a security vulnerability, but it is also possible for malicious actors to use the ME to remotely compromise a system)
- it is possible (but untested and potentially riskier) to use Linux instead of Windows for IVprep (might write a new CT for this topic if there is enough interest)
- the Soft Temporary Disable Mode means the BIOS is only asking (not forcing) Intel ME to disable itself on the next boot, and this mode is preserved between reboots and poweroffs8
- 1vyrain comes with additional BIOS mod features: Overclocking support (35xx, 37xx, 38xx, 39xx CPUs), Whitelist removal to use any WLAN/WWAN adapter, and Advanced menu (custom fan curve, TDP, etc)
- you can also flash custom bios images (coreboot, skulls, heads) with 1vyrain
- advanced users can attempt to build 1vyrain from source9
- Dig deeper: 1vyrain longform FAQ10, Disabling Intel ME 11 via undocumented mode11, Ivy Bridge Lenovo ThinkPad Internal Flashing12, me_cleaner13, tripcode!Q/7’s coreboot(skulls) video14
Feedback
Let me know if you find this helpful and, depending on interest, I will do my best to create more Cypherpunk Transmission reports in the future.
You might have noticed that this wasn’t posted on Monday. Creating CTs is very time consuming (research and testing can take days at times). The fixed schedule is incompatible with the format and puts unencessary pressure on the quality, which I can’t sacrifice for the sake of quota. Consider future CTs on-demand (unscheduled, like meeting summaries).
Questions, edits and suggestions are always appreciated @ /about/.
-3RA
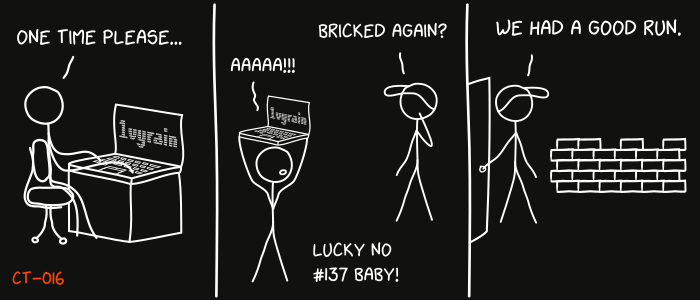
Credit goes to gnuteardrops from monero.graphics for the amazing xkcd graphic. Work and xkcd Script font licensed under CC BY-NC 3.0.
-
https://github.com/gch1p/thinkpad-bios-software-flashing-guide#bios-versions ↩
-
https://drive.google.com/open?id=1yusq98ja6NmI4G4txKVueFqY_ZEwaZvO ↩
-
https://github.com/gch1p/thinkpad-bios-software-flashing-guide#about-intel-me ↩
-
https://medium.com/@n4ru/1vyrain-self-build-documentation-5059825b1fdb ↩
-
https://medium.com/@n4ru/1vyrain-an-xx30-thinkpad-jailbreak-fd4bb0bdb654 ↩
-
https://web.archive.org/web/20201201175708/http://blog.ptsecurity.com/2017/08/disabling-intel-me.html?m=1 ↩
-
https://doc.coreboot.org/mainboard/lenovo/ivb_internal_flashing.html ↩
-
https://github.com/corna/me_cleaner/wiki/How-to-apply-me_cleaner ↩